| Field | Description |
|---|---|
| First Name | Enter user’s first name |
| Last Name | Enter user’s last name |
| Alias | Auto-filled based on name or enter manually |
| Enter user’s email address | |
| Username | Must be in email format, unique across all Salesforce orgs |
| Nickname | Unique name for internal use |
| Role | Select appropriate role (e.g., Sales Rep) |
| User License | Select the appropriate license (e.g., Salesforce) |
| Profile | Select a profile such as Standard User or System Administrator |



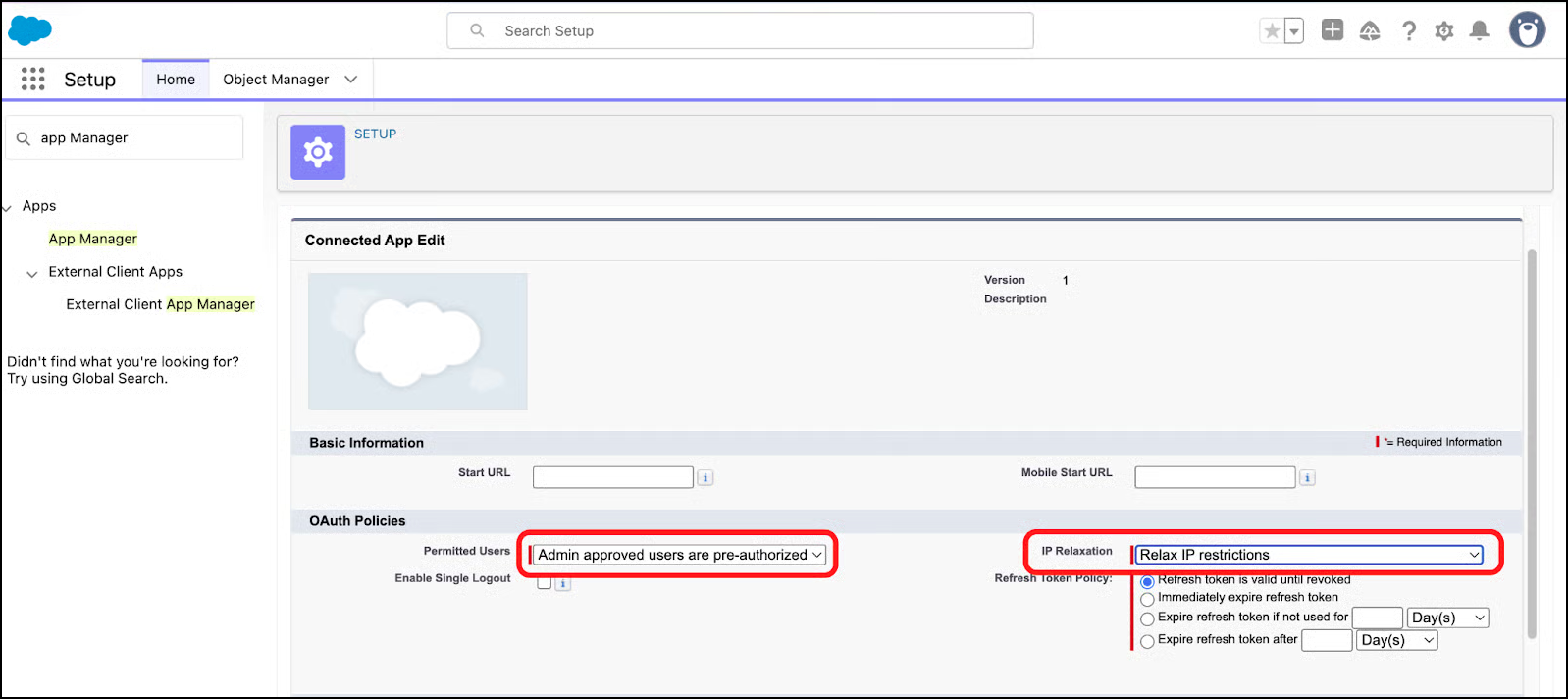
| Setting | Value |
|---|---|
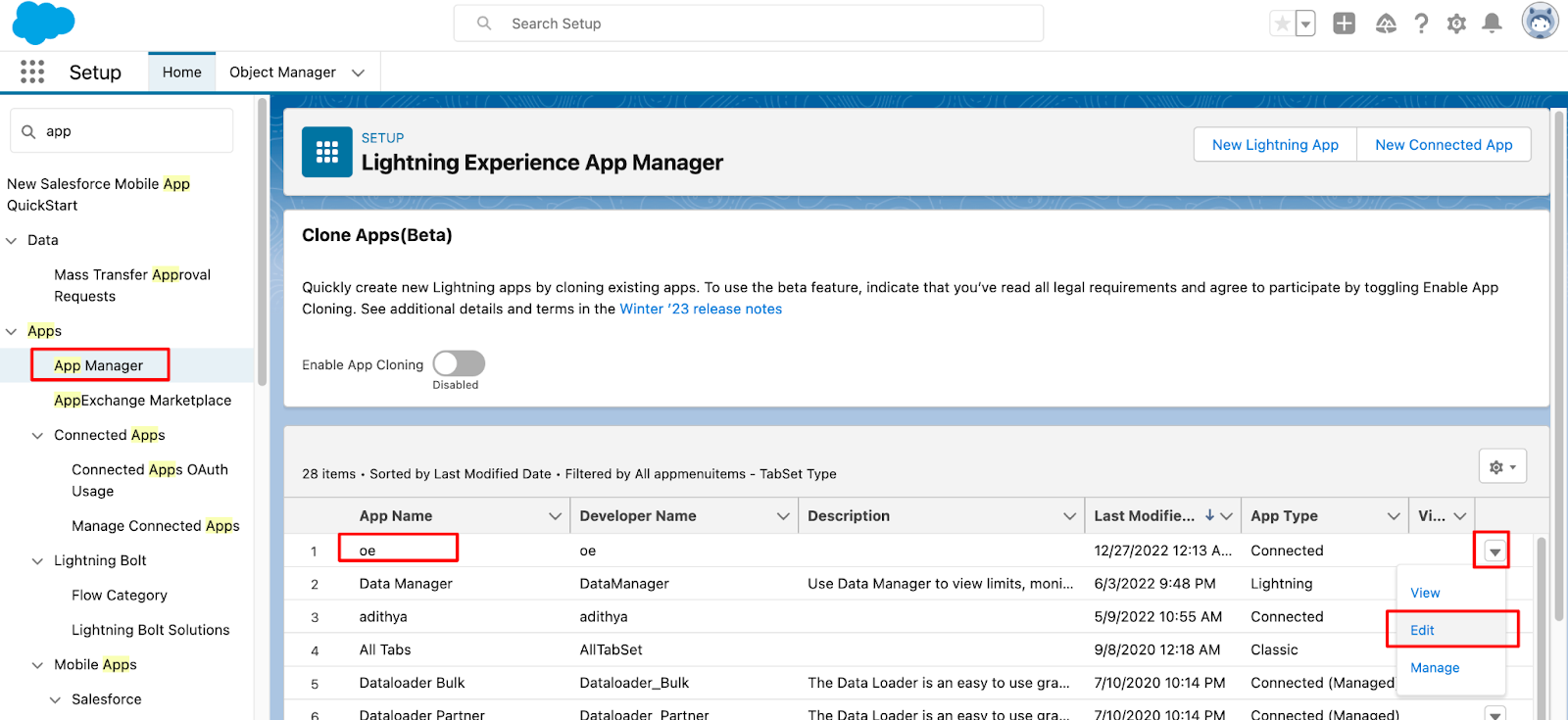
| IP Relaxation | Relax IP restrictions (recommended when the app will be accessed from multiple or dynamic IP addresses) |
| Permitted Users | Admin approved users are pre-authorized (ensures only users with assigned permission sets or profiles can use the app.) |











| Setting Name | Action Required | Notes |
|---|---|---|
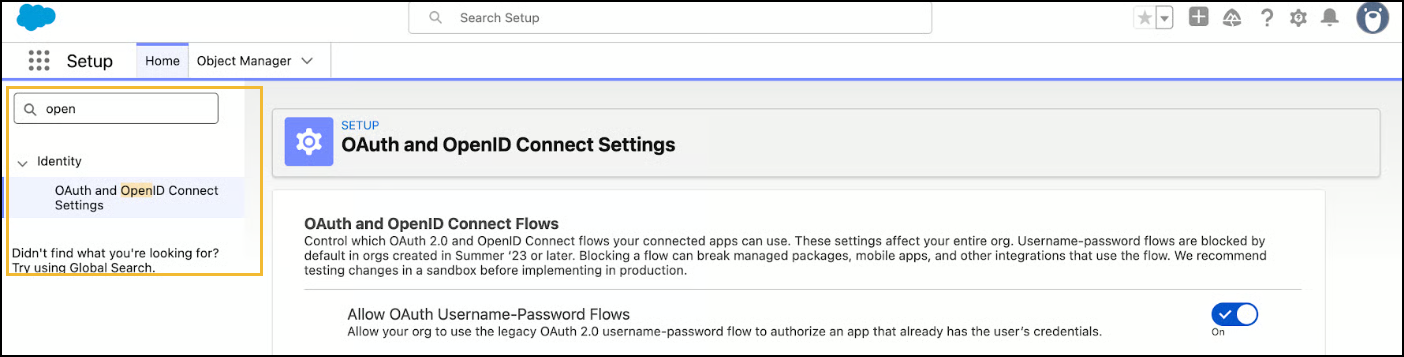
| Allow OAuth Username-Password Flows | Enable if using username/password flow (e.g., scripts, Postman). | This also requires the "Enable Username-Password Flow" setting to be enabled within the Connected App configuration itself. |