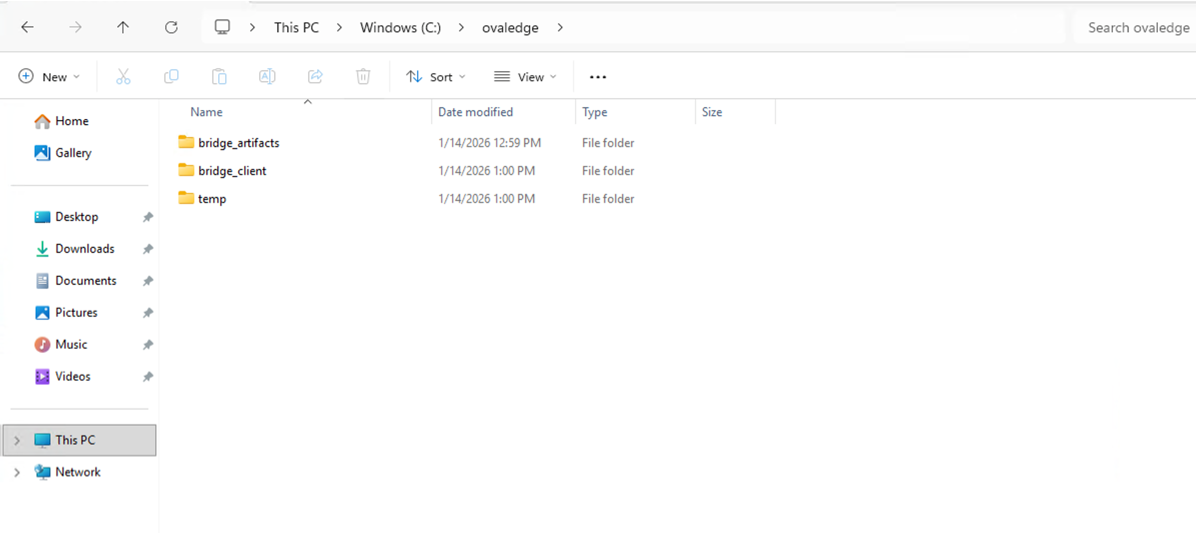
| File Name | Description |
|---|---|
| Bridge Secure Connectivity Pack (.zip) | Contains certificates and configuration files required for secure communication between the Bridge Client and Bridge Server. |
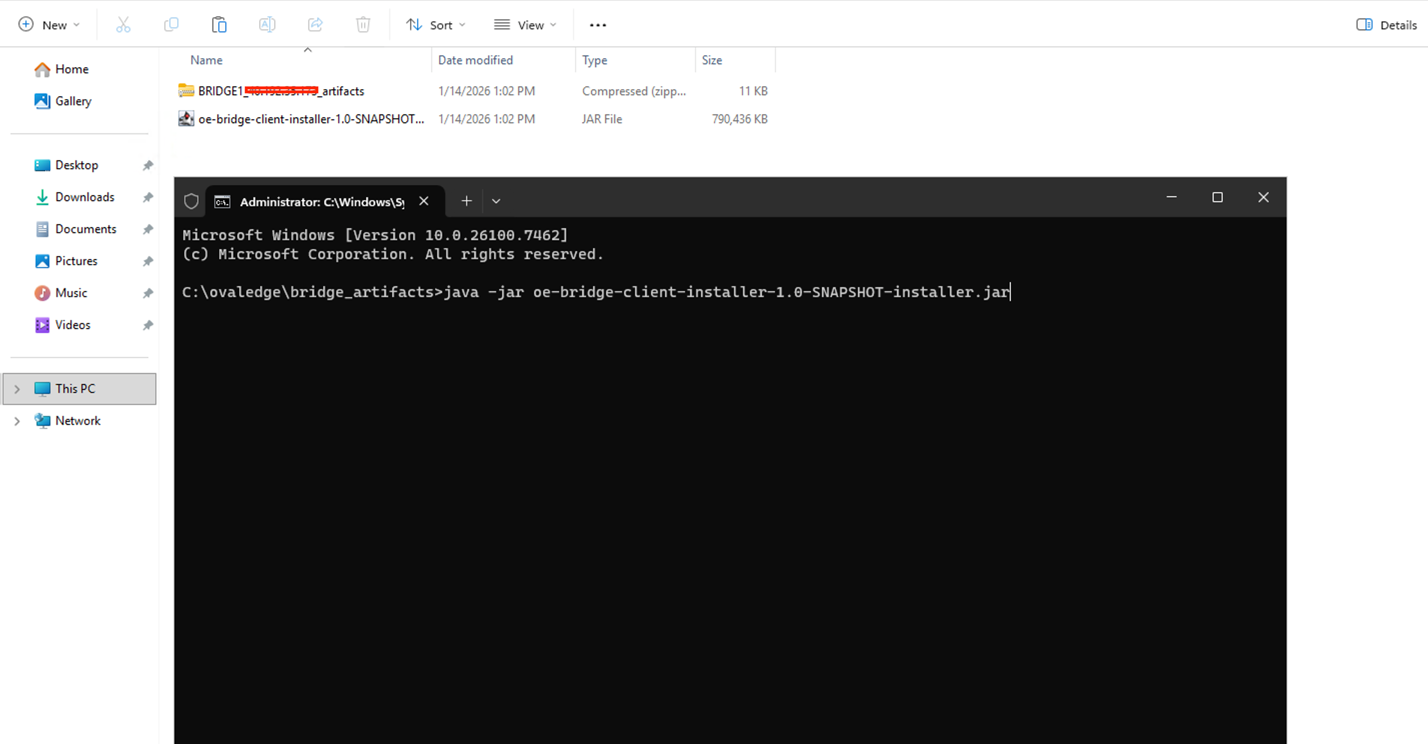
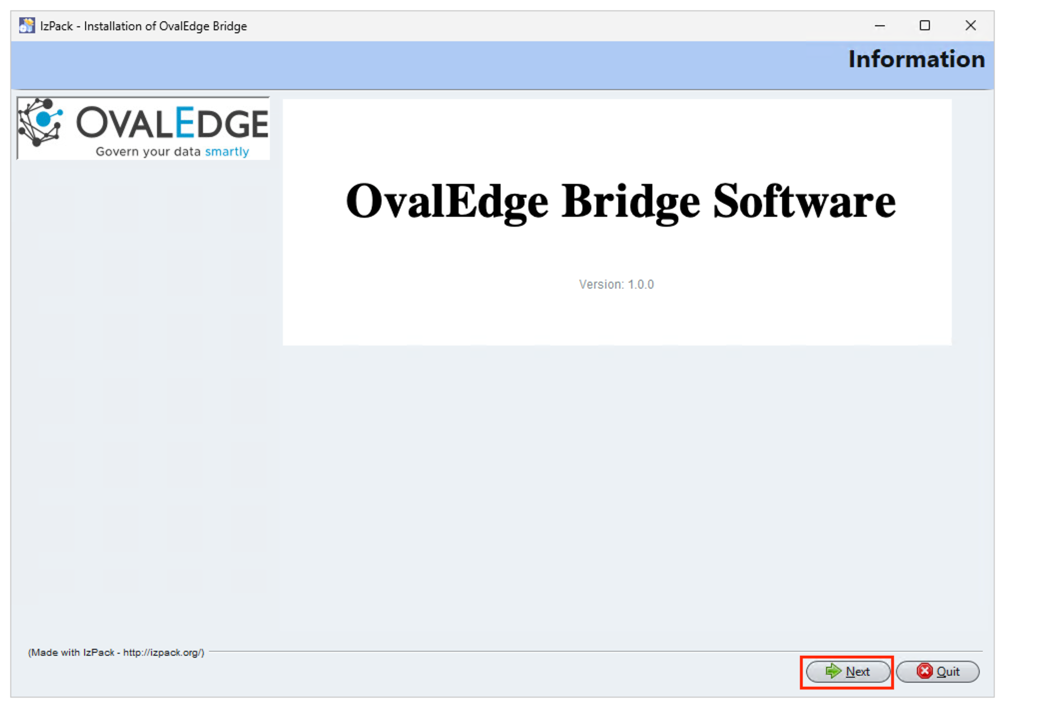
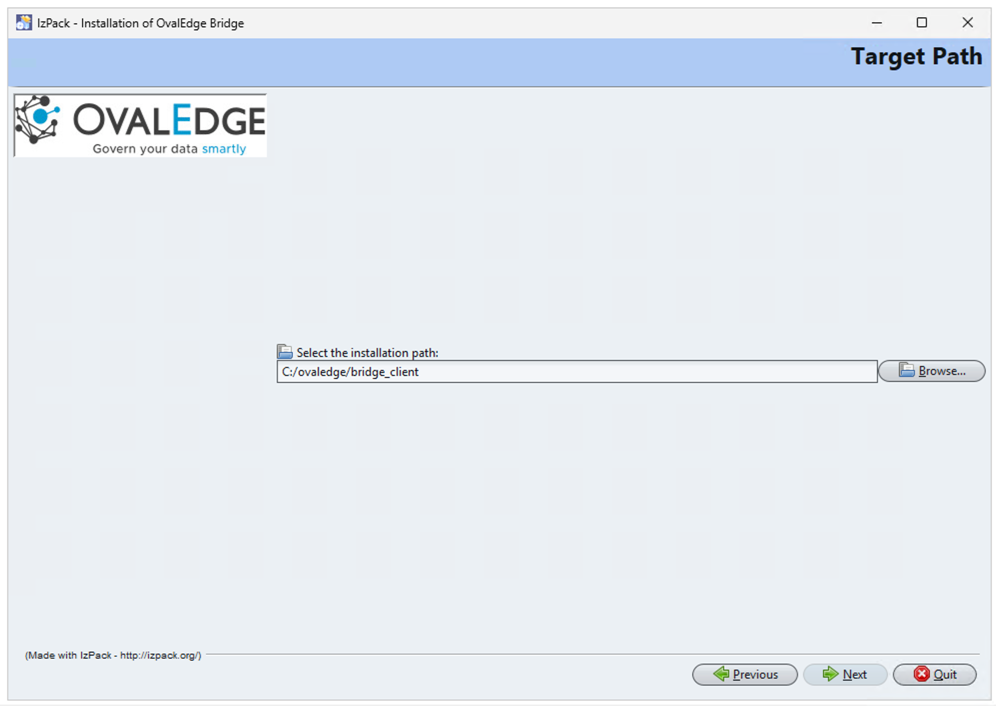
| Bridge Client Installer (.jar) | Required to execute the Bridge Client installation process. |
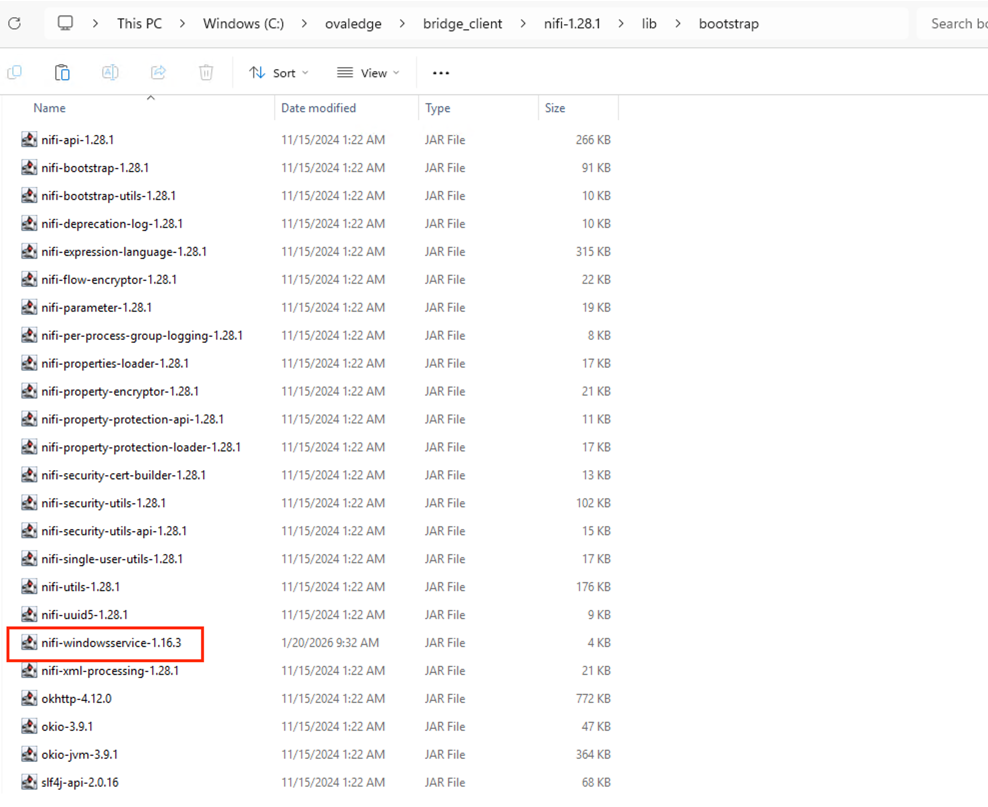
| Bridge Component File (.nar) | Must be placed in the NiFi lib folder after installation to enable communication with the OvalEdge SaaS platform. |
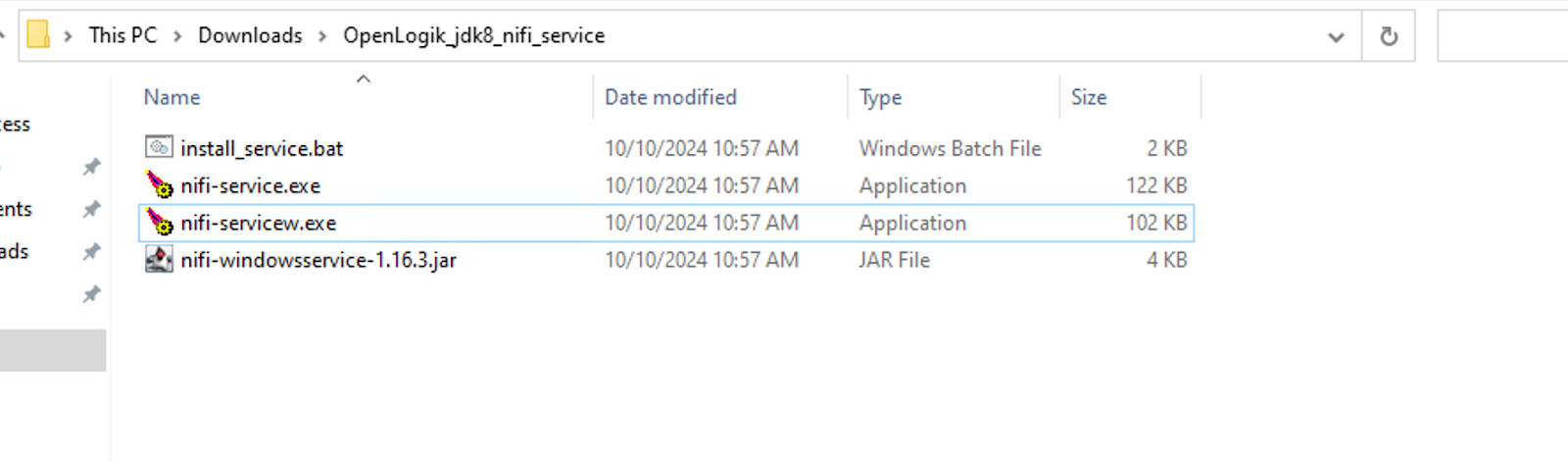
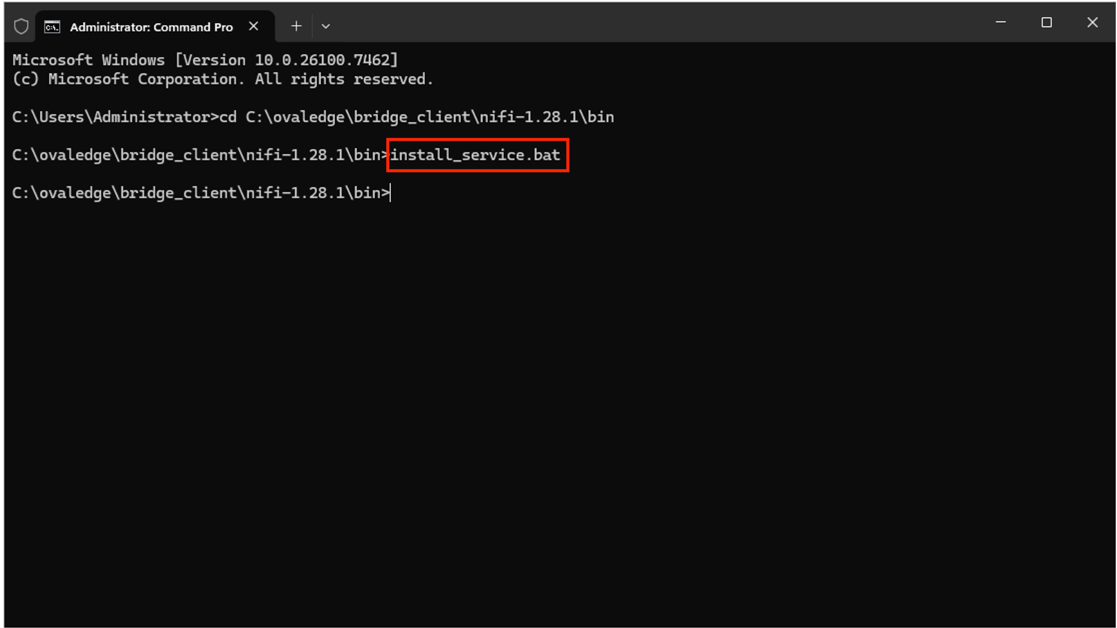
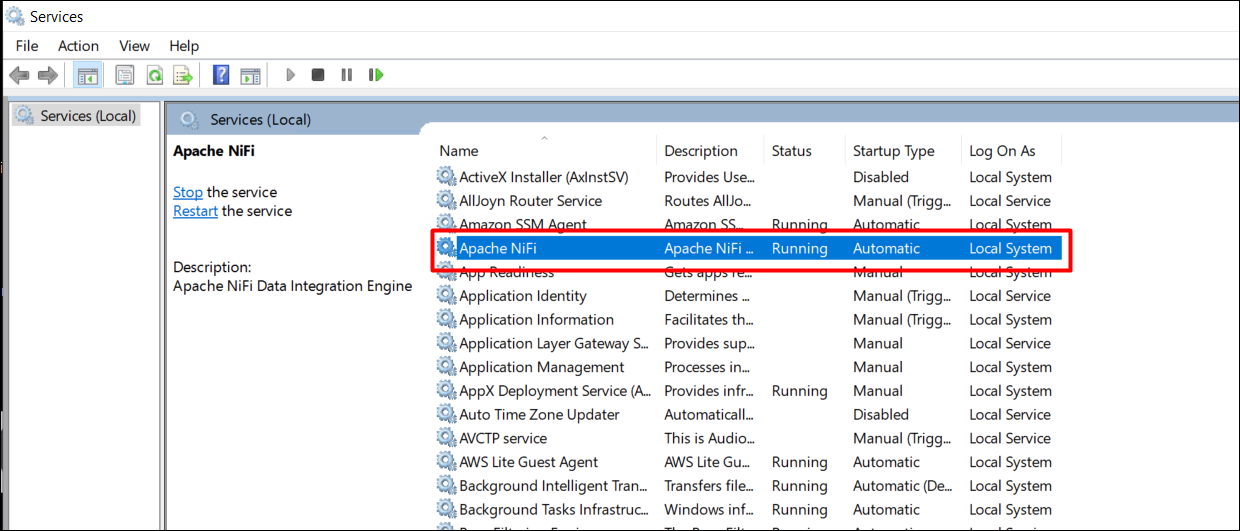
| Bridge As Service Files | Required to run the Bridge process as a service. |
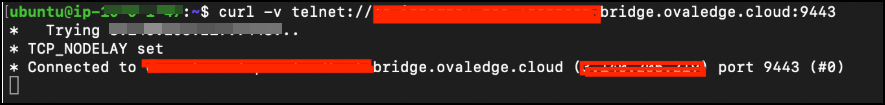
| Port Type | Port | Purpose |
|---|---|---|
| Inbound | 9443 | Required for NiFi UI configuration changes |
| Outbound | 9443 | Communication from Bridge Client to Bridge Server |
| Component | Description |
|---|---|
| Bridge Server | Hosted on the OvalEdge SaaS AWS environment and interacts directly with the OvalEdge platform. |
| Bridge Client | Installed on the client’s infrastructure (cloud or on-premise) and communicates securely with the Bridge Server. |
| Environment | Bridge Server Location | Bridge Client Location | Communication Requirement |
|---|---|---|---|
| Cloud-based Sources | OvalEdge SaaS AWS Server | Public cloud VM (provided by client) | The Client VM IP address must be whitelisted to communicate securely with the Bridge Server hosted on the SaaS VM. |
| On-Premise Sources | OvalEdge SaaS AWS Server | On-prem VM (provided by client) | The Client VM IP address must be whitelisted to communicate securely with the Bridge Server hosted on the SaaS VM. |