| Connector Category | RDBMS |
| OvalEdge Release Supported | Release6.3.4 and later |
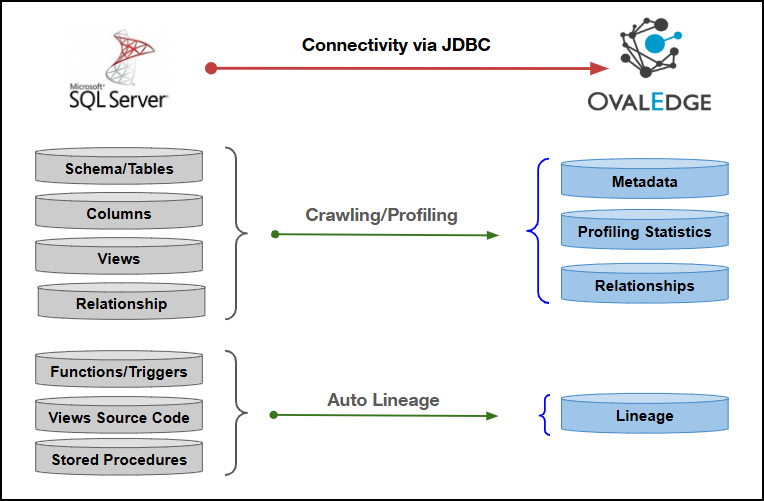
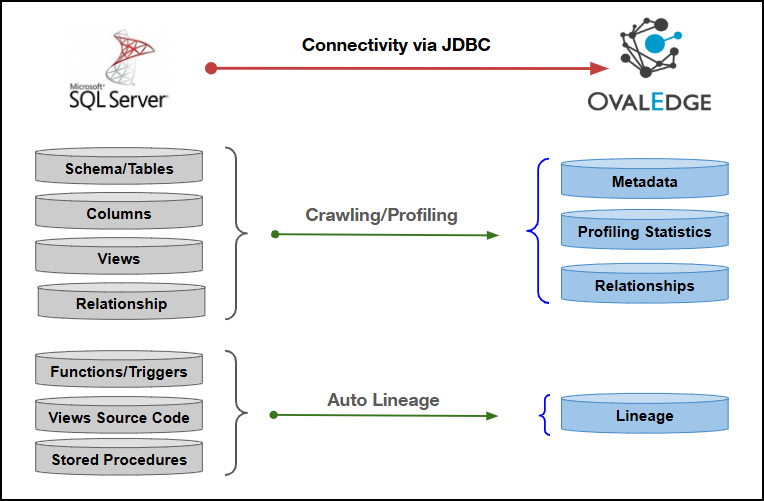
| Connectivity [How the connection is established with Microsoft SQL Server] | JDBC driver |
| Verified Microsoft SQL Server Versions | Microsoft SQL Server 2019 (15.0.4236.7) and later |
| SQL Server Object | SQL Server Property | OvalEdge Attribute | OvalEdge Category | OvalEdge Type |
|---|---|---|---|---|
| Table | Table Name | Table | Tables | Table |
| Table | Table Type | Table | Tables | Table |
| Table | Table Comments | Source Description | Descriptions | Source Description |
| Columns | Column Name | Column | Table Columns | - |
| Columns | Data Type | Column Type | Table Columns | - |
| Columns | Description | Source Description | Table Columns | - |
| Columns | Ordinal Position | Column Position | Table Columns | - |
| Columns | Length | Data Type Size | Table Columns | - |
| Views | View Name | View | Tables | View |
| Views | Text | View Query | Views | View |
| Procedures | Routine_name | Name | Procedures | - |
| Procedures | Description | Source Description | Descriptions | - |
| Procedures | Routine_definition | Procedure | Procedures | - |
| Functions | Routine_name | Name | Functions | - |
| Functions | Routine_definition | Function | Functions | - |
| Functions | Description | Source Description | Descriptions | - |
| Triggers | Trigger Name | Name | Triggers | - |
| Triggers | Trigger Definition | Trigger Data | Triggers | - |
| Triggers | Trigger Type | Type | Triggers | - |
| Operation | Objects | System Tables | Access Permission |
|---|---|---|---|
| Crawling & Profiling | Schema | sys.schemas | SELECT |
| Crawling & Profiling | Schema | extended_properties | SELECT |
| Crawling & Profiling | Tables | information_schema.tables | SELECT |
| Crawling & Profiling | Tables | fn_listextendedproperty | SELECT |
| Crawling & Profiling | Table Columns | sys.all_columns | SELECT |
| Crawling & Profiling | Table Columns | sys.types | SELECT |
| Crawling & Profiling | Table Columns | sys.views | SELECT |
| Crawling & Profiling | Table Columns | information_schema.columns | SELECT |
| Crawling & Profiling | Table Columns | information_schema.key_column_usage | SELECT |
| Crawling & Profiling | Table Columns | information_schema.table_constraints | SELECT |
| Crawling, Profiling & Lineage Building | Views | information_schema.views | View Definition |
| Crawling, Profiling & Lineage Building | Views | sys.objects | View Definition |
| Crawling & Lineage Building | Functions & Stored Procedures Source code | information_schema.routines | View Definition |
| Crawling & Lineage Building | Functions & Stored Procedures Source code | sys.sql_modules | View Definition |
| Crawling & Lineage Building | Functions & Stored Procedures Source code | sys.extended_properties | View Definition |
| Crawling | Triggers | sys.objects | SELECT |
| Crawling | Triggers | sql_modules | SELECT |
| Crawling | Synonyms | sys.synonyms | SELECT |
| Crawling | Relationships | sys.foreign_keys | SELECT |
| Crawling | Indexes | on specified table | View Definition |
| Field Name | Description |
|---|---|
| Connector Type | By default, "SQL Server" is displayed as the selected connector type. |
| Authentication | The following five types of authentication are supported for Microsoft SQL Server:
|
| Field Name | Description |
|---|---|
| Credential Manager* | Select the desired credentials manager from the drop-down list. The corresponding parameters will be displayed based on the selected option. Supported Credential Managers:
|
| License Add Ons |
|
| Connector Name* | Enter a unique name for the Microsoft SQL Server connection (Example: "SQL Server_Prod"). |
| Connector Environment | Select the environment (Example: PROD, STG) configured for the connector. |
| Connector description | Enter a brief description of the connector. |
| Server* | Enter the Microsoft SQL server name or IP address (Example: xxxx-sqlserver.xxxx4ijtzasl.xx-south-1.rds.xxxxxws.com or xxx.xx8.x.10). |
| Port* | By default, the port number for the Microsoft SQL Server, "1433" is auto-populated. If required, the port number can be modified as per custom port number that is configured for the Microsoft SQL Server. |
| Database* | Enter the database name to which the service account user has access within the Microsoft SQL Server. |
| Driver* | By default, the Microsoft SQL Server driver details are auto-populated. |
| Username* | Enter the service account username set up to access the Microsoft SQL Server database (Example: "oesauser"). |
| Password* | Enter the password associated with the service account user. |
| Connection String | Configure the connection string for the Microsoft SQL Server database:
Replace placeholders with actual database details. {sid} refers to Database Name. |
| Plugin Server | Enter the server’s name when running as a plugin server. |
| Plugin Port | Enter the port number on which the plugin is running. |
| Field Name | Description |
|---|---|
| OvalEdge Installed Environment | Select the environment where the application has been installed.
|
| Credential Manager* | Select the desired credentials manager from the drop-down list. The corresponding parameters will be displayed based on the selected option. Supported Credential Managers:
|
| License Add Ons |
|
| Connector Name* | Enter a unique name for the Microsoft SQL Server connection (Example: "SQL Server_Prod"). |
| Connector Environment | Select the environment (Example: PROD, STG) configured for the connector. |
| Connector Description | Enter a brief description of the connector. |
| Server* | Enter the Microsoft SQL Server database server name or IP address (Example: xxxx-sqlserver.xxxx4ijtzasl.xx-south-1.rds.xxxxxnaxxws.com or 1xx.xxx.1.x0). |
| Port* | By default, the port number for the Microsoft SQL Server, "1433" is auto-populated. If required, the port number can be modified as per custom port number that is configured for the Microsoft SQL Server. |
| Database* | Enter the database name to which the service account user has access within the Microsoft SQL Server. |
| Domain | Enter the qualified Microsoft SQL Server domain name. Note: This field appears only when the installation environment is selected as Linux/Unix. |
| Driver* | By default, the Microsoft SQL Server driver details are auto-populated. |
| Username* | Enter the service account username set up to access the Microsoft SQL Server database (Example: "oesauser"). Note: This field appears only when the installation environment is selected as Linux/Unix. |
| Password* | Enter the password associated with the service account user. Note: This field appears only when the installation environment is selected as Linux/Unix. |
| Connection String | Configure the connection string for the Microsoft SQL Server database:
Replace placeholders with actual database details. {sid} refers to Database Name. |
| Plugin Server | Enter the server’s name when running as a plugin server. |
| Plugin Port | Enter the port number on which the plugin is running. |
| Field Name | Description |
|---|---|
| Credential Manager* | Select the desired credentials manager from the drop-down list. The corresponding parameters will be displayed based on the selected option. Supported Credential Managers:
|
| License Add Ons |
|
| Connector Name* | Enter a unique name for the Microsoft SQL Server connection (Example: "SQL Server_Prod"). |
| Connector Environment | Select the environment (Example: PROD, STG) configured for the connector. |
| Connector Description | Enter a brief description of the connector. |
| Server* | Enter the Microsoft SQL Server database server name or IP address (Example: xxxx-sqlserver.xxxx4ijtzasl.xx-south-1.rds.xxxxxnaws.com or 1xx.xxx.1.x0). |
| Port* | By default, the port number for the Microsoft SQL Server, "1433" is auto-populated. If required, the port number can be modified as per custom port number that is configured for the Microsoft SQL Server. |
| Database* | Enter the database name to which the service account user has access within the Microsoft SQL Server. |
| Driver* | By default, the Microsoft SQL Server driver details are auto-populated. |
| Username* | Enter the service account username set up to access the Microsoft SQL Server database (Example: "oesauser"). |
| Password* | Enter the password associated with the service account user. |
| Connection String | Configure the connection string for the Microsoft SQL Server database:
Replace placeholders with actual database details. {sid} refers to Database Name. |
| Plugin Server | Enter the server’s name when running as a plugin server. |
| Plugin Port | Enter the port number on which the plugin is running. |
| Field Name | Description |
|---|---|
| Credential Manager* | Select the desired credentials manager from the drop-down list. The corresponding parameters will be displayed based on the selected option. Supported Credential Managers:
|
| License Add Ons |
|
| Connector Name* | Enter a unique name for the Microsoft SQL Server connection (Example: "SQL Server_Prod"). |
| Connector Environment | Select the environment (Example: PROD, STG) configured for the connector. |
| Connector Description | Enter a brief description of the connector. |
| Managed Identity Client Id* | Enter the Client ID of the User Assigned Managed Identity configured in Azure. |
| Server* | Enter the Microsoft SQL Server database server name or IP address (Example: xxxx-sqlserver.xxxx4ijtzasl.xx-south-1.rds.xxxxxnaws.com or 1xx.xxx.1.x0). |
| Database* | Enter the database name to which the service account user has access within the Microsoft SQL Server. |
| Driver* | By default, the Microsoft SQL Server driver details are auto-populated. |
| Connection String | Configure the connection string for the Microsoft SQL Server database:
Replace placeholders with actual database details. {sid} refers to Database Name. |
| Plugin Server | Enter the server’s name when running as a plugin server. |
| Plugin Port | Enter the port number on which the plugin is running. |
| Field Name | Description |
|---|---|
| Credential Manager* | Select the desired credentials manager from the drop-down list. The corresponding parameters will be displayed based on the selected option. Supported Credential Managers:
|
| License Add Ons |
|
| Connector Name* | Enter a unique name for the Microsoft SQL Server connection (Example: "SQL Server_Prod"). |
| Connector Environment | Select the environment (Example: PROD, STG) configured for the connector. |
| Connector Description | Enter a brief description of the connector. |
| Server* | Enter the Microsoft SQL Server database server name or IP address (Example: xxxx-sqlserver.xxxx4ijtzasl.xx-south-1.rds.xxxxxnaws.com or 1xx.xxx.1.x0). |
| Port* | By default, the port number for the Microsoft SQL Server, "1433" is auto-populated. If required, the port number can be modified as per custom port number that is configured for the Microsoft SQL Server. |
| Database* | Enter the database name to which the service account user has access within the Microsoft SQL Server. |
| Client Id* | Enter the Azure AD Application (Service Principal) Client ID used for authentication. |
| Client Secret* | Enter the Client Secret associated with the Azure AD application. |
| Tenant ID* | Enter the Azure AD Tenant ID where the Service Principal is registered. |
| Driver* | By default, the Microsoft SQL Server driver details are auto-populated. |
| Connection String | Configure the connection string for the Microsoft SQL Server database:
Replace placeholders with actual database details. {sid} refers to Database Name. |
| Plugin Server | Enter the server’s name when running as a plugin server. |
| Plugin Port | Enter the port number on which the plugin is running. |
| Default Governance Roles* | Select the appropriate users or teams for each governance role from the drop-down list. All users configured in the security settings are available for selection. |
| Admin Roles* | Select one or more users from the dropdown list for Integration Admin and Security & Governance Admin. All users configured in the security settings are available for selection. |
| No Of Archive Objects* | This shows the number of recent metadata changes to a dataset at the source. By default, it is off. To enable it, toggle the Archive button and specify the number of objects to archive. Example: Setting it to 4 retrieves the last four changes, displayed in the 'Version' column of the 'Metadata Changes' module. |
| Select Bridge* | If applicable, select the bridge from the drop-down list. The drop-down list displays all active bridges that have been configured. These bridges facilitate communication between data sources and the system without requiring changes to firewall rules. |
| S. No. | Error Message(s) | Error Description & Resolution |
|---|---|---|
| 1 | Error while validating connection: Exception occurred while validating in SQL Server Connection: Failed to obtain JDBC Connection; nested exception is com.microsoft.sqlserver.xxx.SQxxxxrException: Login failed for user 'xxxxx'. ClientConnectionId: 9xxxxx2-6xxx-4xx2-xx13-xxxx846xx | Error Description: Either username and password might be wrong. Resolution:
|
| 2 | invalid DB Error while validating connection. Error:Exception occured while validating in SQL Server Connection: Failed to obtain JDBC Connection; nested exception is com.microsoft.sqlserver.xxx.SQLxxxException: Cannot open database "xxx" requested by the login. The login failed. ClientConnectionId:1xxxxx7a- xxxa-4xx9-bxxx-xxxxxx6bxxx7 | Error Description: The database name provided is invalid. Resolution:
|
| 3 | The TCP/IP connection to the host <HOSTNAME>, port 1433 has failed. Error: "connect timed out. Verify the connection properties." | Error Description:
|
| 4 | Login failed for user 'test_user'. User does not have permission to perform this action. | Error Description:
|
| 5 | Invalid object name 'sys.masked_columns'. | Error Description:
|
| 6 | Cannot find the object 'sp_myproc' because it does not exist or you do not have permissions. | Error Description:
|
| 7 | Could not get JDBC Connection; nested exception is java.sql.SQLException: The TCP/IP connection to the host .. | Error Description:
|