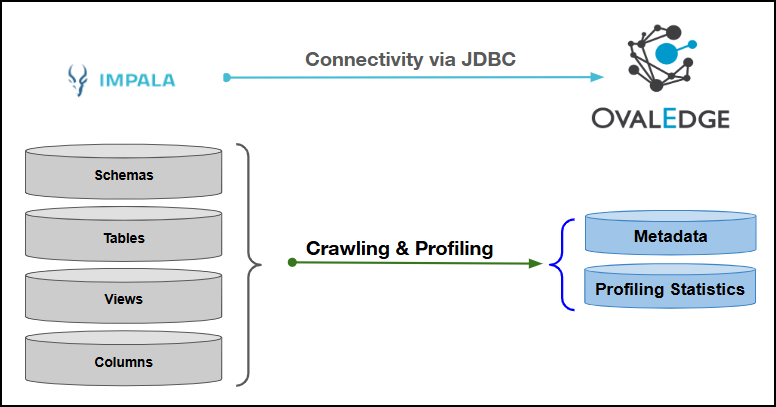
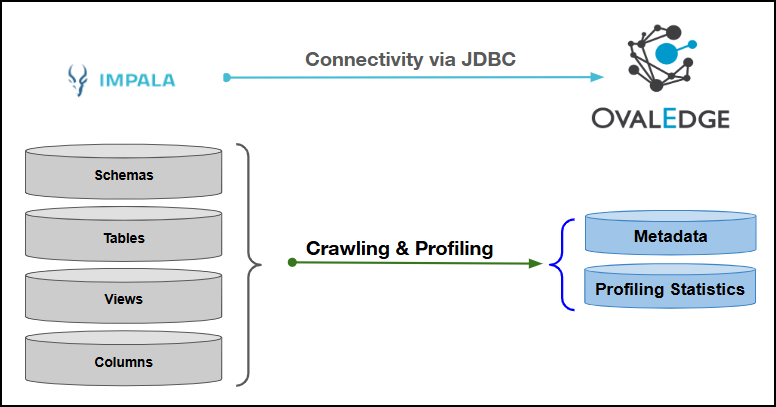
Connectivity
\[How the connection is established with Apache Impala]
| JDBC | | Verified Apache Impala Version | 2.5.31 | ### Connector Features | Feature | Availability | | -------------------------------------------- | :----------: | | Crawling | ✅ | | Delta Crawling | ❌ | | Profiling | ✅ | | Query Sheet | ✅ | | Data Preview | ✅ | | Auto Lineage | NA | | Manual Lineage | ✅ | | Secure Authentication via Credential Manager | ✅ | | Data Quality | ❌ | | DAM (Data Access Management) | ❌ | | Bridge | ✅ | {% hint style="info" %} 'NA' indicates that the respective feature is 'Not Applicable.' {% endhint %} ### Metadata Mapping The following objects are crawled from the Apache Impala and mapped to the corresponding UI assets.| Apache Impala Object | Apache Impala Attribute | OvalEdge Attribute | OvalEdge Category | OvalEdge Type |
|---|---|---|---|---|
| Schema | Schema name | Schema | Databases | Schema |
| Table | Table Name | Table | Tables | Table |
| Table | Table Type | Type | Tables | Table |
| Table | Table Comments | Source Description | Descriptions | Source Description |
| Columns | Column Name | Column | Table Columns | Columns |
| Columns | Data Type | Column Type | Table Columns | Columns |
| Columns | Description | Source Description | Table Columns | Columns |
| Views | View Name | View | Tables | Views |
| Field Name | Description |
|---|---|
| Connector Type | By default, "Apache Impala" is displayed as the selected connector type. |
| Authentication* | The following two types of authentication are supported for Apache Impala Server:
|
| Field Name | Description |
|---|---|
| Credential Manager* | Select the desired credentials manager from the drop-down list. Relevant parameters will be displayed based on the selection. Supported Credential Managers:
|
| Connector Name* | Enter a unique name for the Apache Impala connection (Example: "Apache Impala_Prod"). |
| Connector Environment | Select the environment (Example: PROD, STG) configured for the connector. |
| Connector Description | Enter the description related to the connector. |
| Server* | Enter the IP address of the server where Apache Impala is hosted. |
| Port* | Apache Impala uses port 21050 by default. The port number can be modified as needed. |
| Database* | The ‘Database’ field specifies the default schema to connect to within the Impala server. Example: If the target database is sales_db, enter sales_db to connect directly instead of the default schema. |
| Driver* | By default, Apache Impala uses ‘com.cloudera.impala.jdbc41.Driver.’ This field is not editable. |
| Principal | The Principal field specifies the Kerberos principal that the client will use to authenticate to the Impala service. It identifies the service account for Impala in the Kerberos realm. |
| Connection String | Configure the connection string for the Impala server:
Replace placeholders with actual server details:
Authentication Plugins: This is the default authentication string used for connecting to Impala. The principal parameter specifies the Impala service principal for authentication. |
| Keytab | The Keytab field specifies the path to the Kerberos keytab file containing the principal’s credentials. It is used to securely authenticate the client to the Impala server without manual password entry. |
| Krb5-Configuration File* | The Krb5-Configuration File field specifies the path to the krb5.conf file used for Kerberos authentication. It provides the necessary Kerberos realm and KDC information for Impala to validate the user's credentials. |
| Plugin Server | Enter the server name when running as a plugin server. |
| Plugin Port | Enter the port number on which the plugin is running. |
| Field Name | Description |
|---|---|
| Credential Manager* | Select the desired credentials manager from the drop-down list. Relevant parameters will be displayed based on the selection. Supported Credential Managers:
|
| Connector Name* | Enter a unique name for the Apache Impala connection (Example: "Apache Impala_Prod"). |
| Connector Environment | Select the environment (Example: PROD, STG) configured for the connector. |
| Connector Description | Enter the description related to the connector. |
| Server* | Enter the IP address of the server where Apache Impala is hosted. |
| Port* | Apache Impala uses port 21050 by default. The port number can be modified as needed. |
| Database* | The ‘Database’ field specifies the default schema to connect to within the Impala server. Example: If the target database is sales_db, enter sales_db to connect directly instead of the default schema. |
| Driver* | By default, Apache Impala uses ‘com.cloudera.impala.jdbc41.Driver.’ This field is not editable. |
| Username* | The username field specifies the user account used to connect to the Impala server. |
| Password* | The Password field should contain the user’s password associated with the provided username. It is used to authenticate the connection when establishing a session with the Impala server. |
| Connection String | Configure the connection string for the Impala server:
Replace placeholders with actual server details:
Authentication Plugins: This is the default authentication string used for connecting to Impala. The principal parameter specifies the Impala service principal for authentication. |
| Plugin Server | Enter the server name when running as a plugin server. |
| Plugin Port | Enter the port number on which the plugin is running. |
| Default Governance Roles* | Select the appropriate users or teams for each governance role from the drop-down list. All users and teams configured in OvalEdge Security are displayed for selection. |
| Admin Roles* | Select one or more users from the dropdown list for Integration Admin and Security & Governance Admin. All users configured in OvalEdge Security are available for selection. |
| No Of Archive Objects* | This shows the number of recent metadata changes to a dataset at the source. By default, it is off. To enable it, toggle the Archive button and specify the number of objects to archive. Example: Setting it to 4 retrieves the last four changes, displayed in the 'Version' column of the 'Metadata Changes' module. |
| Select Bridge* | If applicable, select the bridge from the drop-down list. The drop-down list displays all active bridges configured in OvalEdge. These bridges enable communication between data sources and OvalEdge without altering firewall rules. |
| S.No. | Error Message(s) | Error Description & Resolution |
|---|---|---|
| 1 | Handler dispatch failed: java.lang.NoSuchFieldError: DEFAULT_MAX_WAIT | Description: This error occurs when the Impala connector (or a dependent library, such as the JDBC/ODBC driver or Hadoop/Hive libraries) tries to access a field named DEFAULT_MAX_WAIT that does not exist in the loaded version of the class. Resolution: Ensure that the Impala JDBC/ODBC driver version matches the Impala server version. Confirm that any Hadoop/Hive libraries on the classpath are compatible with the connector. |